Advanced IT Hub 514485116 recognizes the critical need for a solid security framework amidst rising cyber threats. The organization employs cutting-edge technologies such as biometric authentication and cloud encryption to bolster access control. Additionally, ongoing employee training enhances awareness and vigilance. However, the complexity of modern cyber risks necessitates a closer examination of both proactive measures and incident response strategies. What challenges lie ahead for maintaining security in this evolving landscape?
The Importance of Security at Advanced IT Hub 514485116
Given the increasing complexity of cyber threats, the security of Advanced IT Hub 514485116 is paramount for safeguarding sensitive data and maintaining operational integrity.
Effective risk management strategies must be employed to mitigate vulnerabilities.
Security awareness among employees is critical, as human error remains a significant factor in breaches.
A robust security framework fosters a culture of vigilance, ultimately enhancing the Hub’s resilience against evolving threats.
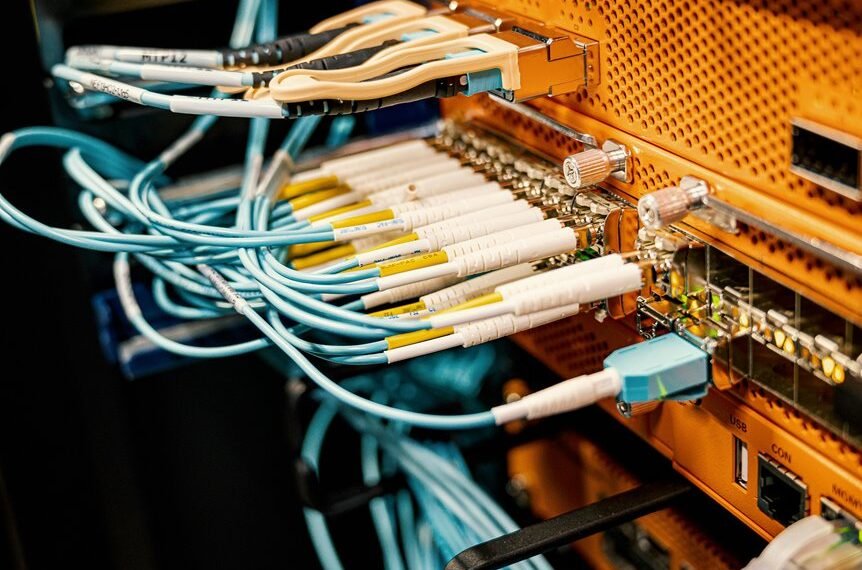
Innovative Technologies for Enhanced Protection
As the threat landscape evolves, Advanced IT Hub 514485116 must leverage innovative technologies to bolster its security posture.
Implementing biometric authentication enhances access control by ensuring that only authorized users can engage with sensitive data.
Additionally, cloud encryption secures information in transit and at rest, safeguarding against unauthorized access.
Together, these technologies provide a robust framework for maintaining data security in an increasingly complex environment.
Best Practices for Maintaining Data Integrity
While organizations strive to enhance their security measures, maintaining data integrity remains a critical component of any comprehensive information security strategy.
Effective practices include implementing rigorous data validation protocols to ensure accuracy and consistency.
Additionally, employing robust encryption techniques safeguards data against unauthorized access, thus preserving its integrity.
Adhering to these best practices empowers organizations to uphold trust and reliability in their information systems.
Responding to Threats: Incident Response Strategies
Data integrity practices lay the foundation for an effective incident response strategy.
A comprehensive threat assessment identifies vulnerabilities, enabling organizations to prioritize risks.
Response planning must encompass clear protocols, ensuring rapid mobilization of resources during incidents.
Conclusion
As the cyber landscape evolves, Advanced IT Hub 514485116 stands at a critical juncture, fortified by innovative technologies and a vigilant workforce. However, lurking in the shadows are increasingly sophisticated threats, ready to exploit any weakness. The organization’s commitment to continuous improvement and proactive measures is commendable, yet the question remains: will these defenses hold firm against the next wave of cyber onslaughts? Only time will reveal the resilience of their security framework in this relentless battle.