Advanced IT Services 627970238 Security emphasizes the critical need for resilient cloud infrastructure in today’s digital landscape. Its approach integrates incident response frameworks and continuous threat monitoring, allowing organizations to swiftly address security vulnerabilities. This method not only protects digital assets but also aligns with data protection regulations. Yet, the effectiveness of such strategies raises questions about their implementation and the broader implications for organizational trust and efficiency. What factors influence their success?
Understanding the Importance of IT Security for Businesses
As organizations increasingly rely on digital infrastructure, the significance of IT security becomes paramount.
Effective risk management strategies are essential to mitigate potential threats, while comprehensive employee training enhances awareness and responsiveness to security breaches.
Key Features of Advanced IT Services 627970238
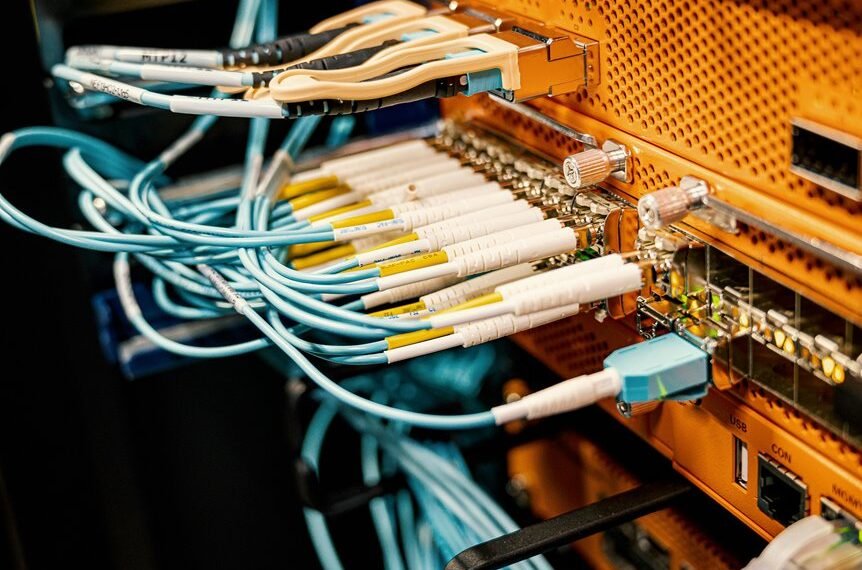
Advanced IT services encompass a range of critical features designed to enhance organizational security and operational efficiency.
Key components include robust cloud infrastructure, facilitating data accessibility and scalability while maintaining security standards.
Additionally, an effective incident response framework is essential, enabling rapid identification and mitigation of security breaches.
These features collectively empower organizations to operate securely in a dynamic digital landscape, fostering resilience and adaptability.
How Does Proactive Threat Detection Work in Advanced IT Security?
How can organizations effectively anticipate and neutralize emerging threats within their IT environments?
Proactive threat detection operates through continuous threat monitoring, employing advanced algorithms to identify anomalies and potential vulnerabilities.
By leveraging real-time data analysis, organizations can enhance incident response capabilities, enabling swift mitigation of identified threats.
This approach minimizes risk exposure, fostering a resilient security posture that empowers organizations to safeguard their digital assets effectively.
Ensuring Compliance With Data Protection Regulations
Proactive threat detection not only enhances an organization’s ability to respond to immediate security incidents but also plays a critical role in ensuring compliance with data protection regulations.
Conclusion
In an era where cyber threats loom like storm clouds on the horizon, Advanced IT Services 627970238 Security acts as a robust lighthouse, guiding organizations through turbulent waters. By implementing proactive threat detection and ensuring compliance with data protection regulations, businesses can navigate challenges with confidence. Just as a seasoned sailor anticipates changing tides, organizations equipped with these advanced security measures can swiftly adapt, safeguarding their digital assets and fostering enduring trust with stakeholders amidst uncertainty.